How to Use The Mac OS X Hackers Toolbox When you think of an operating system to run pen testing tools on, you probably think of Linux and more specifically BackTrack Linux. BackTrack Linux is a great option and one of the most common platforms for running pen testing tools. If you are a Mac user, then. Our software library provides a free download of Hacker Menu 1.1.5 for Mac. Our built-in antivirus scanned this Mac download and rated it as virus free. This free software for Mac OS X was originally produced by jingweno & lokywin. The program lies within Lifestyle Tools. John the Ripper. John the Ripper is one of the most popular password crackers of all time.
When talking about different OS platforms like Windows, Linux or Mac OS X, the common term that we can get to hear is Hacking. These operating systems are easily prone to hacking and have the highest records of being hacked by professional hackers. Since it involves a great level of skill and knowledge on computer and its networks, not many of us are aware of hacking and how they actually do it. However, there exists some exciting hacking tools 2018 that are required to become a successful hacker. Here we bring you some of the best hacking tools of 2018 along with its best features. Read on the guide to make use of the information for educational purpose rather than for malicious practice. Get to know the detailed information of these best ethical hacking tools 2018 and learn how to use the hacking tools. Along with these best hacking tools for Windows, Linux and Mac OS X, also have a look at the best Android hacking apps 2018.
NetSparker
Maintaining improper security breaches means that you are keeping your business at risk in the near future. NetSparker is more than a best hacking tool as it works as a web application security tool to manage security vulnerabilities. The built-in workflow tools are designed specifically to manage the security of multiple websites. You need not buy, install any hardware or software, just launch the application from the dashboard to perform a security scan from any location. If it is unable to check any flaw, it will just warn you of something malicious activity happening. Moreover, it automatically exploits the vulnerabilities found in a safe way and even display the proof of exploitation thus warning us to use more advanced security settings.
Download NetSparker.
Nmap (Network Mapper)
The best hacking tools 2018 till date that is feature-rich and at the same offers user-friendly interface is Nmap. With its advanced tools, Nmap is sure to keep all the hackers behind. The Nmap that is called as Network Mapper is the free open source hacking tool used for network scanning and security auditing. Considering its features, the Nmap is claimed to be one of the best ethical hacking tools 2018. With thousands of admin users, Nmap has the capability to discover open ports, monitor host availability on the network and also can determine which operating system is used by the host system. This award-winning hacking tool renders its support to all major platforms like Windows, Linux and Mac OS X.
Here is how to connect remotely on Windows 10.
Download Nmap (Network Mapper).
MetaSploit
The fully featured hacking tool that can hack like a pro is Metasploit. Designed for enterprise security solutions, the Metasploit can test your defence attacks on the network safely and helps to uncover all those security issues if any. Rather than calling as a Metasploit, it can be called as a collection of exploits with its own infrastructure to build its own custom tools. It is one of the popular security tools to locate vulnerabilities on Windows, Linux, Mac OS X. It can simulate the real-world attacks thus making you know about your weak points so as to fix them at priority. This tool is quite helpful for the penetration testers and for those professionals involved in IDS testing plans.
Download MetaSploit.
Wireshark
Available for free download, the Wireshark hacking tools 2018 is a packet sniffer, packet analyzer and a password hacker. Apart from capturing and detecting network passwords, the Wireshark holds the capability to secure the network from outside intruders. Not only the offline analysis, Wireshark can also analyze data from Bluetooth, USB, Token ring, Ethernet and more. Supporting all major platforms, this is one of the best ethical hacking tools 2018 available online. It can inspect hundreds of protocols and detects best results with live capture.
Also read: How to run Windows programs without installing them.
Install GIPHY: The GIF Search Engine. If for some reason you don't already have this amazing app. Make animated gif mac. Tons of awesome wallpapers GIF to download for free. You can also upload and share your favorite wallpapers GIF. HD wallpapers and background images. Mac: Sick of using those boring, static images as your wallpaper. If you want to spice things up a bit, the GIFPaper app can set any GIF as a wallpaper.
Download Wireshark.
Maltego
Here is another best hacking tools 2018 that is available for Windows, Linux and Mac Operating system. This interactive hacking tool is used for interrogation to find the relationship between information collected from different sources. It can depict the information graphically and analyses the relationship between different entities like websites, documents, people and companies. It can enumerate network information such as DNS name, domain name, IP address, and netblocks. As for the personal information, Maltego can analyze email address, phone numbers, social groups that the person is associated with and the list of companies that the person is in connection with. It can even extract metadata from the target domain files. With the easy to use interface, you can install the Maltego setup quickly and immediately provides the graphical interface to see the relationships instantly. If your PC or laptop is running on Windows, Linux or Mac OS X then probably this is one of the best ethical hacking tools 2018 to consider.
Download Maltego.
Acunetix WVS
The automated tool that can scan web applications and resolve the exploitable vulnerabilities is Acunetix WVS. Considering the innovative features offered, this is one of the best hacking tools 2018 attracted by many hackers. Securing the web application of the company especially from the professional hackers is quite a tedious task. As the Cyber attacks are taking a rise, the need for the best ethical hacking tools 2018 has become mandatory. Here comes the need pf Acunetix WVS that is designed by keeping the threat in mind. It can scan as well as resolve any exploitable vulnerabilities. Developed by highly experienced security developers, this renders its support to all the major Operating system platforms.
Download Acunetix WVS.
Want to download the Windows latest version, then check here for Windows 10 latest version free download 2018, Lucky Patcher 7.2.9 APK Latest Version so, have a look at the best Antivirus to install for Windows 10 operating system.now it is possible to run windows programs without installing them.If ads and pop up’s are irritating you then have a look at AdBlock Vs AdBlock Plus – Which Is The Better Ad Blocker 2018.
PreviousNext
In past decades, ethical hacking and penetration testing were performed by only a few security experts. Now almost anyone can report security incidents. Ethical hacking tools allow you to scan, search and find the flaws and vulnerabilities within any company to help make their systems and applications more secure (as seen in the recent Top CVE’s exploited in the wild post published a few weeks ago).
Today we’ll explore the best ethical hacking tools used by modern security researchers.
15 Ethical Hacking Tools You Can’t Miss
We’ve compiled some of the most popular penetration testing tools to help you through the first steps of a security investigation. You’ll find some of the classic tools that seem to have been around forever and some new tools that might not be familiar.
1. John the Ripper
John the Ripper is one of the most popular password crackers of all time. It’s also one of the best security tools available to test password strength in your operating system, or for auditing one remotely.
This password cracker is able to auto-detect the type of encryption used in almost any password, and will change its password test algorithm accordingly, making it one of the most intelligent password cracking tools ever.
This ethical hacking tool uses brute force technology to decipher passwords and algorithms such as:
- DES, MD5, Blowfish
- Kerberos AFS
- Hash LM (Lan Manager), the system used in Windows NT / 2000 / XP / 2003
- MD4, LDAP, MySQL (using third-party modules)
Another bonus is that JTR is open source, multi-platform and fully available for Mac, Linux, Windows and Android.
Stay in the loop with the best infosec news, tips and tools
Follow us on Twitter to receive updates!
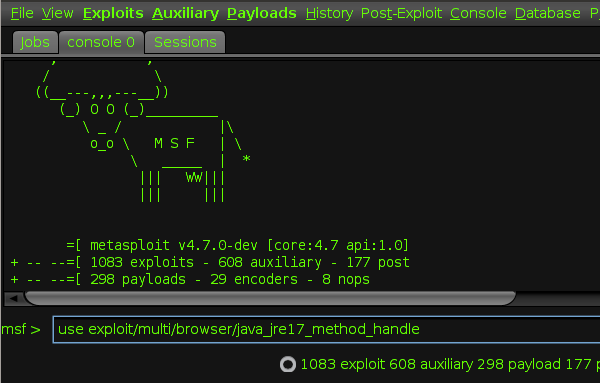
2. Metasploit
Metasploit is an open source cyber-security project that allows infosec professionals to use different penetration testing tools to discover remote software vulnerabilities. It also functions as an exploit module development platform.
One of the most famous results of this project is the Metasploit Framework, written in Ruby, which enables you to develop, test and execute exploits easily. The framework includes a set of security tools that can be used to:
- Evade detection systems
- Run security vulnerability scans
- Execute remote attacks
- Enumerate networks and hosts
Metasploit offers three different versions of their software:
- Pro: ideal for penetration testing and IT security teams.
- Community: used by small companies and infosec students.
- Framework: the best for app developers and security researchers.
Supported platforms include:
- Mac OS X
- Linux
- Windows
3. Nmap
Nmap (Network Mapper) is a free open source security tool used by infosec professionals to manage and audit network and OS security for both local and remote hosts.
Despite being one of the oldest security tools in existence (launched in 1997), it continues to be actively updated and receives new improvements every year.
It’s also regarded as one of the most effective network mappers around, known for being fast and for consistently delivering thorough results with any security investigation.
What can you do with Nmap?
- Audit device security
- Detect open ports on remote hosts
- Network mapping and enumeration
- Find vulnerabilities inside any network
- Launch massive DNS queries against domains and subdomains
Supported platforms include:
- Mac OS X
- Linux, OpenBSD and Solaris
- Microsoft Windows
4. Wireshark
Wiresharkis a free open-source software that allows you to analyze network traffic in real time. Thanks to its sniffing technology, Wireshark is widely known for its ability to detect security problems in any network, as well as for its effectiveness in solving general networking problems.
While sniffing the network, you’re able to intercept and read results in human-readable format, which makes it easier to identify potential problems (such as low latency), threats and vulnerabilities.
Main features:
- Saves analysis for offline inspection
- Packet browser
- Powerful GUI
- Rich VoIP analysis
- Inspects and decompresses gzip files
- Reads other capture files formats including: Sniffer Pro, tcpdump (libpcap), Microsoft network monitor, Cisco Secure IDS iplog, etc.
- Supported ports and network devices: Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI.
- Protocol decryption includes but not limited to IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP, and WPA/WPA2
- Exports results to XML, PostScript, CSV, or plain text
Wireshark supports up to 2000 different network protocols, and is available on all major operating systems including:
- Linux
- Windows
- Mac OS X
- FreeBSD, NetBSD, OpenBSD
5. OpenVAS
OpenVAS (also known as the old classic “Nessus”) is an open-source network scanner used to detect remote vulnerabilities in any hosts. One of the best-known network vulnerability scanners, it’s very popular among system administrators and DevOps and infosec professionals.
Main features
- Powerful web-based interface
- +50,000 network vulnerability tests
- Simultaneous multiple host scanning
- Able to stop, pause and resume scan tasks
- False positive management
- Scheduled scans
- Graphics and statistics generation
- Exports results to plain text, XML, HTML or LateX
- Powerful CLI available
- Fully integrated with Nagios monitoring software
While its web-based interface allows it to be run from any operating system, a CLI is also available and works well for Linux, Unix and Windows operating systems.
The free version can be downloaded from the OpenVAS website, but there is also a commercial enterprise license available from the Greenbone Security (parent company) website.
6. IronWASP
If you’re going to perform ethical hacking, IronWASP is another great tool. It’s free, open source and multi-platform, perfect for those who need to audit their web servers and public applications.
One of the most appealing things about IronWASP is that you don’t need to be an expert to manage its main features. It’s all GUI-based, and full scans can be performed in only a few clicks. So, if you’re just getting started with ethical hacking tools, this is a great way to start.
Some of its main features include:
- Powerful GUI-based interface
- Web scan sequence recording
- Exports results into HTML and RTF file format
- 25+ different web vulnerabilities
- False positive and negative management
- Full Python and Ruby support for its scripting engine
- Can be extended by using modules written in C#, Ruby, and Python
- Supported platforms: Windows, Linux with Wine, and MacOS using CrossOver
7. Nikto
Nikto is another favorite, well-known as part of the Kali Linux Distribution. Other popular Linux distributions such as Fedora already come with Nikto available in their software repositories as well.
This security tool is used to scan web servers and perform different types of tests against the specified remote host. Its clean and simple command line interface makes it really easy to launch any vulnerability testing against your target, as you can see in the following screenshot:
Nikto’s main features include:
- Detects default installation files on any OS
- Detects outdated software applications.
- Runs XSS vulnerability tests
- Launches dictionary-based brute force attacks
- Exports results into plain text, CSV or HTML files
- Intrusion detection system evasion with LibWhisker
- Integration with Metasploit Framework
8. SQLMap
sqlmap is a cool cyber-security tool written in Python that helps security researchers to launch SQL code injection tests against remote hosts. With SQLMap you can detect and test different types of SQL-based vulnerabilities to harden your apps and servers, or to report vulnerabilities to different companies.
Its SQL injection techniques include: Error 1 while launching tuxera ntfs for mac installer package windows 10.
- UNION query-based
- time-based blind
- boolean-based blind
- error-based
- stacked queries
- out-of-band
Main features:
Pro Tools Mac Os
- Multiple database server support: Oracle, PostgreSQL, MySQL and MSSQL, MS Access, DB2 or Informix.
- Automatic code injection capabilities
- Password hash recognition
- Dictionary-based password cracking
- User enumeration
- Get password hashes
- View user privileges and databases
- Database user privilege escalation
- Dump table information
- Executes remote SQL SELECTS
Check out the next video to see the true power of SQLMap using the sqlmap out-of-band injection working with Metasploit integration against Microsoft SQL Server:
9. SQLNinja
SQLNinja is another SQL vulnerability scanner bundled with Kali Linux distribution. This tool is dedicated to target and exploit web apps that use MS SQL Server as the backend database server. Written in Perl, SQLNinja is available in multiple Unix distros where the Perl interpreter is installed, including:

- Linux
- Mac OS X & iOS
- FreeBSD
SQLninja can be run in different types of modes such as:
- Test mode
- Verbose mode
- Fingerprint remote database mode
- Brute force attack with a word list
- Direct shell & reverse shell
- Scanner for outbound ports
- Reverse ICMP Shell
- DNS tunnelled shell
10. Wapiti
How To Update Mac Os X
Wapiti is a free open-source command-line based vulnerability scanner written in Python. While it’s not the most popular tool in this field, it does a good job of finding security flaws in many web applications.
Using Wapiti can help you to discover security holes including:
- XSS attacks
- SQL injections
- XPath injections
- XXE injections
- CRLF injections
- Server side request forgery

Other features include:
- Runs in verbose mode
- Ability to pause and resume scans.
- Highlights vulnerabilities found inside the terminal
- Generates reports and export into HTML, XML, JSON and TXT
- Activates and deactivates multiple attack modules
- Removes parameters from certain URLs
- Excludes URLs during an attack
- Bypasses SSL certificate verification
- URL extractor from javascript
- Timeout configuration for large scans
- Sets custom user-agent and HTTP headers
11. Maltego
Maltego is the perfect tool for intel gathering and data reconnaissance while you’re performing the first analysis of your target.
In this case, it can be used to correlate and determine relationships between people, names, phone numbers, email addresses, companies, organizations and social network profiles.
Along with online resources like Whois data, DNS records, social networks, search engines, geolocation services and online API services it can also be used to investigate the correlation between internet-based infrastructures including:
- Domain names
- DNS servers
- Netblocks
- IP addresses
- Files
- Web Pages
Main features include:
- GUI-based interface
- Analyzes up to 10.000 entities per graph
- Extended correlation capabilities
- Data sharing in real time
- Correlated data graphics generator
- Exports graphs to GraphML
- Generates entity lists
- Can copy and paste information
This application is available for Windows, Linux, and Mac OS, and the only software requirement is to have Java 1.8 or greater installed.
12. AirCrack-ng
AirCrack-ng is a respected Wifi security suite for home and corporate security investigations. It includes full support for 802.11 WEP and WPA-PSK networks and works by capturing network packets. It then analyzes and uses them to crack Wifi access.
Hi BAMLondon,Based on your description, If Lync Web App Plug-in installation has timed out or failed. Microsoft lync download.
For old-school security professionals, AirCrack-ng includes a fancy terminal-based interface along with a few more interesting features.
Main features:
- Extensive documentation (wiki, manpages)
- Active community (forums and IRC channels)
- Support for Linux, Mac and Windows Wifi detection
- Launches PTW, WEP and Fragmentation attacks
- Supports WPA Migration Mode
- Fast cracking speed
- Multiple Wifi card support
- Integration with 3rd party tools
As a bonus, it comes bundled with a lot of Wifi auditing tools including:
- airbase-ng
- aircrack-ng
- airdecap-ng
- airdecloak-ng
- airdriver-ng
- aireplay-ng
- airmon-ng
- airodump-ng
- airolib-ng
- airserv-ng
- airtun-ng
- easside-ng
- packetforge-ng
- tkiptun-ng
- wesside-ng
- airdecloak-ng
13. Reaver
Reaver is a great open-source alternative to Aircrack-ng that allows you to audit the security of any Wifi with WPA/WPA2 pass keys. It uses brute force Wifi attack techniques like Pixie dust attacks to crack Wifi-protected setups through common Wifi flaws and vulnerabilities.
Depending on how well-configured the router-level Wifi security is, it can take between 3 to 10 hours to get an effective brute-force cracking result.
Until recently, the original Reaver version was hosted at Google Cloud. After the release version of version 1.6,a forked community edition was launched in Github.
Build-time dependencies
- build-essential
- libpcap-dev
Runtime-time dependencies
- pixiewps (required for pixiedust attack)
It runs well on most Linux distributions.
14. Ettercap
Ettercap is a network interceptor and packet sniffer for LAN networks. It supports active and passive scans as well as various protocols, including encrypted ones such as SSH and HTTPS.
Other capabilities include network and host analysis (like OS fingerprint), as well as network manipulation over established connections -- which makes this tool great for testing man-in-the-middle attacks.
Main features
- Active and passive protocol analysis
- Filters based on IP source and destination, Mac and ARP addresses
- Data injection into established connections
- SSH and HTTPS encryption-based protocols
- Sniffs remote traffic over GRE tunnel
- Extensible with plugins
- Protocol supports include Telnet, FTP, Imap, Smb, MySQL, LDAP, NFS, SNMP, HTTP, etc.
- Determines OS name and version
- Able to kill established LAN connections
- DNS Hijacking
15. Canvas
Canvas is a great alternative to Metasploit, offering more than 800 exploits for testing remote networks.
Main features
- Remote network exploitation
- Targets different kind of systems
- Targets selected geographic regions
- Takes screenshots of remote systems
- Downloads passwords
- Modifies files inside the system
- Escalates privileges to gain administrator access
This tool also lets you use its platform to write new exploits or use its famous shellcode generator. It also integrates an alternative to nmap called scanrand, which is especially useful for port scanning and host discovery over mid to large networks.
Supported platforms include:
- Linux
- MacOSX (requires PyGTK)
- Windows (requires Python and PyGTK)
Summary
Software companies reap the most benefits from the rise of automated ethical hacking tools and penetration testing utilities, giving them more ways to increase system security every day.
Automated tools are changing the way hacking is evolving, making ethical penetration testing easier, faster and more reliable than ever. Penetration testing and reporting activities now play a crucial role in the process of identifying security flaws in remote or local software — enabling company owners to quickly prevent vulnerabilities from running wild all over the Internet.
Like many of these valuable tools, we’ve developed SecurityTrails from scratch, combining different domain automation lists and tons of forensic data so you can audit your domain names, DNS and online applications.
Are you ready to unveil the true power of our security toolkit? Grab a free API account today or contact us for consultation.

Os X Version Mac
Do you want to access the ultimate OSINT tool?Fill out the form to learn how SurfaceBrowser™ can help you to explore Domains, DNS Servers, IP addresses and much more.